Understanding OAuth 2.1 for MCP (Model Context Protocol) Server: Discovery, Authorization, and Access Phases
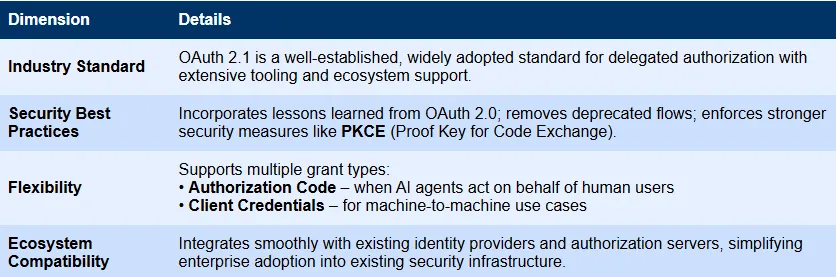
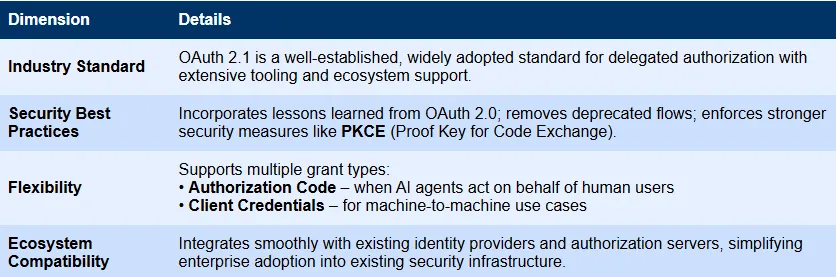
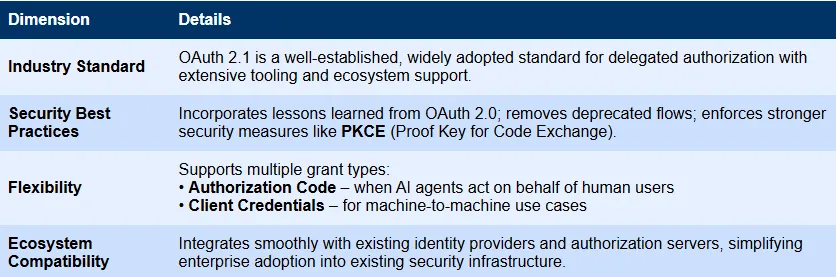
OAuth 2.1 is a formally required authorization standard in the Model Context Protocol (MCP) specification. According to official documents, authorized servers must provide confidential and public customers with appropriate security measures to implement OAuth 2.1.
MCP provides authorization at the shipping level, allowing customers to securely access restricted servers on behalf of resource owners. OAuth 2.1 was chosen as the framework for MCP because it provides a modern, secure and standardized approach to management authorization.
How the authorization process works
The MCP authorization flow is designed to ensure secure and controlled access to protected servers. It occurs in three main stages:
Discovery phase
When an MCP client tries to connect to a protected server, the server responds with an unauthorized state of 401 and a www-partententicate header pointing to its authorized server. The client then uses the metadata provided by the authorization server to discover its functionality and learn how to authenticate.
Authorization phase
Once the client understands how the server handles authorization, it begins the registration and authorization process.
if Dynamic Customer Registration Supported, clients can automatically register on the authorized server without manual settings. In this step, the client provides basic details such as its name, type, redirect URL and required scope. In response, the authorization server issues client_id and client_secret to the client credentials (usually client_id and client_secret) that the client will use in subsequent requests. This process makes new customers faster and more scalable, especially in large or automated environments.
After registration, the client begins the appropriate OAuth process:
- Authorized Code Flow – Used when acting on behalf of human users.
- Customer Credentials Flow – Used for secure machine communication.
In the authorization code flow, users are required to approve and agree. After approval, the authorization server issues an access token and uses the appropriate scope for the customer to use.
Visit phase
After mastering the access token, the client sends it and its requests and their requests to the MCP server. The server verifies the token, checks the scope, then processes the request and returns the response. Each interaction in the process is documented on auditing and compliance to ensure security and traceability.
Key security enhancements in MCP OAUTH 2.1
The MCP authorization specification includes several important security upgrades to make the process safer and more reliable:
Mandatory PKCE
All MCP customers must use PKCE (Proof key for code exchange) is as defined in OAuth 2.1. PKCE adds a layer of protection by creating a secret “Verifier-Challenge” pair to ensure that only the original client that initiates the request can exchange the authorization code for the token. This prevents attacks such as code interception or injection.
Strict redirect URI verification
The client must pre-log out of its exact redirect URI with the authorization server. When authorization occurs, the server checks for the exact match. This prevents attackers from redirecting the token to an unauthorized location.
A brief token
Authorized servers are encouraged to issue temporary access tokens. If the token is accidentally exposed or stolen, its short lifespan can reduce the risk of abuse.
Grain range model
MCP OAUTH 2.1 allows fine element permissions to use the oscilloscope, so customers can only access what they need. Examples include:
MCP: Tools: Weather – Use weather tools only.
MCP: Resources: Customer Data: Reading – Read customer data access only.
MCP: Execution: Workflow:* – Allows any workflow to run.
Dynamic Customer Registration
MCP clients and servers can support automatic client registration. This allows new customers to obtain their credentials (such as customer ID) without manual settings, making it faster and easier to securely join new AI agents.
How to implement OAuth 2.1 for MCP server
In the next part of this article, we will dig deeper into how to implement OAuth 2.1 for MCP servers. We will create a simple financial sentiment analysis server and implement authorization using ScaleKit to simplify the entire process.

I am a civil engineering graduate in Islamic Islam in Jamia Milia New Delhi (2022) and I am very interested in data science, especially neural networks and their applications in various fields.


